In the ever-evolving landscape of cybersecurity, new threats emerge that can compromise the digital integrity of individuals and organizations alike. One such threat that has gained attention is the VenomSoftX malware, often associated with the counter.wmail-service.com virus. In this article, we’ll delve into the details of this malicious software, its potential impact, and the steps you can take to safeguard yourself against it.
In other words, the digital age of online security is paramount, and ensuring your system is free from potential threats is crucial. One such concern is the counter.wmail-service.com virus, a potentially harmful program that can compromise your browsing experience and put your data at risk. In this article, we delve into the details of the counter.wmail-service.com virus, its potential risks, and the steps you can take to remove it and safeguard your digital space.

What is Counter.wmail-service.com?
In the ever-evolving digital landscape, safeguarding your online presence is paramount. A name that’s been causing quite a stir in cybersecurity circles is “Counter.wmail-service.com.” This seemingly harmless domain has been revealed as the command and control (C&C) server for a highly sophisticated malware called VenomSoftX. Picture this server as the mastermind’s control centre, where cyber attackers orchestrate their moves and keep a watchful eye on their targets. VenomSoftX, also known as Turla or Snake, is the culprit behind this menace.
What makes VenomSoftX truly chilling is its JavaScript-based Remote Access Trojan nature and its appetite for cryptocurrency theft. This malicious code prowls in the shadows, silently infiltrating systems and giving cybercriminals an invisible gateway to your data. It’s like a digital chameleon, evading detection while wreaking havoc under the surface. Once inside, it can pilfer cryptocurrencies – the digital gold of our times. It’s a stark reminder of the importance of staying vigilant and fortified against these cunning threats.
Understanding VenomSoftX Malware and Counter.wmail-service.com Virus
VenomSoftX malware, colloquially referred to as a virus, is a type of malicious software designed by cybercriminals to infiltrate computer systems and networks. One of its iterations is linked with the counter.wmail-service.com domain, which is commonly used as a command-and-control (C2) server by the malware’s operators.

This malware primarily spreads through deceptive tactics like phishing emails, malicious downloads, or compromised websites. Once it gains access to a system, it can execute a range of malicious activities, such as data theft, remote control of the compromised device, and propagation to other connected systems.
Potential Impact of VenomSoftX Malware
The VenomSoftX malware can have severe consequences for both individuals and businesses:
- Data Breaches: Cybercriminals can use malware to steal sensitive information such as personal credentials, financial data, and intellectual property, leading to identity theft and financial losses.
- Ransomware Attacks: In some cases, VenomSoftX might be a precursor to ransomware attacks. Attackers can encrypt valuable data and demand a ransom for its release.
- Botnet Formation: Malware-infected devices can be harnessed to form a botnet, which can be employed for launching large-scale cyberattacks, like Distributed Denial of Service (DDoS) attacks.
- System Disruption: The malware’s presence can slow down or disrupt system performance, leading to operational inefficiencies.
Protecting Yourself Against VenomSoftX Malware
While the VenomSoftX malware poses a threat, there are measures you can take to safeguard your digital environment:
- Stay Vigilant: Be cautious when opening email attachments or clicking on links, especially if they’re from unknown senders. Verify the legitimacy of the source before taking any action.
- Use Reliable Security Software: Install reputable antivirus and anti-malware software to detect and neutralize potential threats. Keep your security software updated for the latest protection.
- Regular Updates: Keep your operating system, applications, and security software up to date to patch any vulnerabilities that malware might exploit.
- Firewall and Network Security: Enable firewalls and use secure networks, especially when handling sensitive data or conducting online transactions.
- User Training: Educate yourself and your employees about safe online practices, including how to identify phishing attempts and suspicious links.
- Backup Your Data: Regularly back up your important data to an external and secure location. This can help mitigate the impact of a potential ransomware attack.
The counter.wmail-service.com (Virus Removal)
The counter.wmail-service.com virus is classified as a browser hijacker, a type of malware that can alter your browser settings without your consent. It often infiltrates systems through bundled software, deceptive downloads, or malicious links. Once present, it may change your default search engine, homepage, or new tab page, redirecting your online searches to its search results, which may be loaded with ads and sponsored content.
The Risks Associated:
While the counter.wmail-service.com virus may not be as severe as ransomware or other high-level malware, it poses several risks that can negatively impact your online experience. These risks include:
- Privacy Concerns: Browser hijackers may collect and transmit your browsing data, including search queries, visited websites, and personal information. This data can be exploited for targeted advertising or potentially shared with third parties.
- Compromised Search Results: The altered search results provided by the virus may lead you to websites that host malicious content or attempt to trick you into downloading more harmful software.
- Reduced Browsing Performance: Browser hijackers can slow down your browsing experience by redirecting you to unwanted websites, loading excessive ads, and consuming system resources.
Removing the counter.wmail-service.com Virus: Step 1
- Update Security Software: Ensure your antivirus and anti-malware software is up to date. Run a thorough scan of your system to identify and eliminate any threats.
- Run a Full Scan: Perform a comprehensive system scan to identify the malicious files associated with Counter. wmail-service VenomSoftX. This scan casts a spotlight on the hidden corners of your system, where malware might be lurking.
- Quarantine and Remove: Once the scan is complete, your security software will likely flag the malicious files. Quarantine and subsequently remove these files to eliminate the threat.
- Uninstall Suspicious Programs: Go to your computer’s Control Panel or Settings and uninstall any unfamiliar or suspicious programs that might have introduced the virus.
- Remove Browser Extensions: Access your browser’s settings and review the installed extensions. Remove any extensions you didn’t intentionally install or those associated with the counter.wmail-service.com virus.
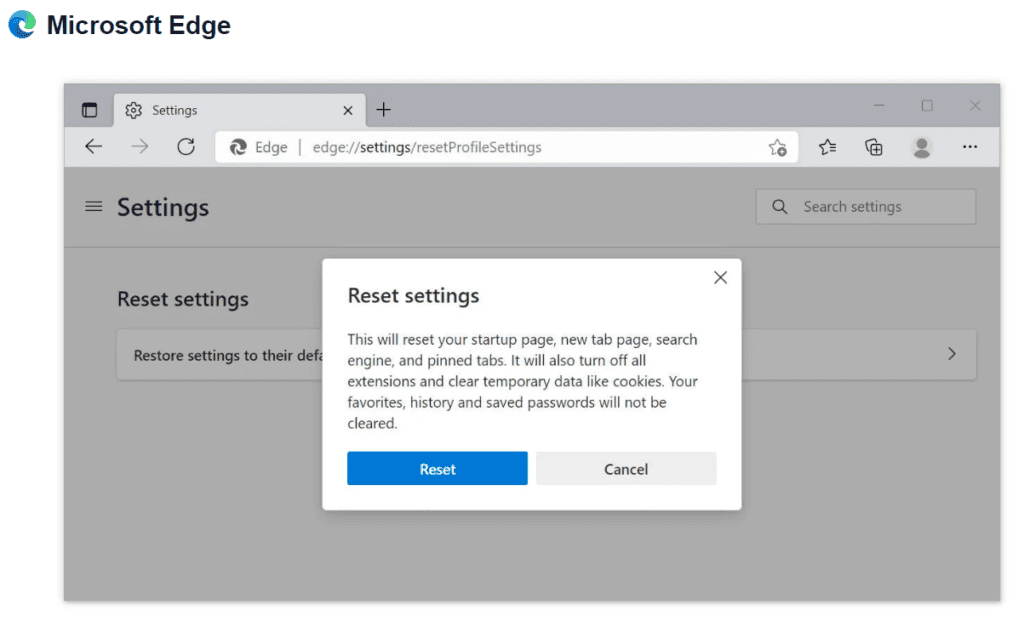
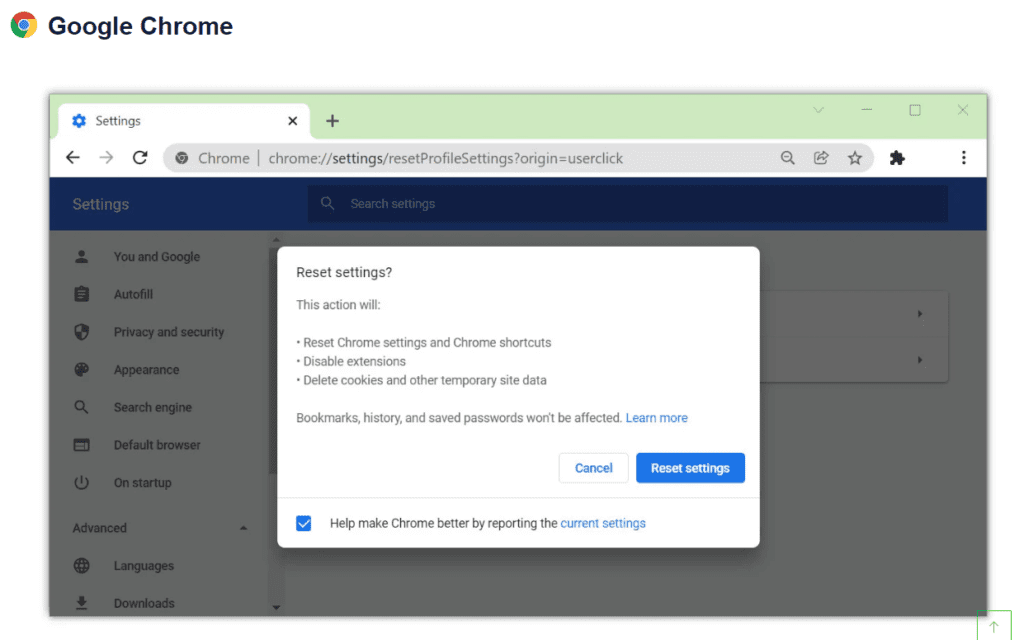
Step 2: How to remove the Counter.wmail-service VenomSoftX?
- Reset Browser Settings: To fully remove the virus’s effects, reset your browser settings to their default state. This will remove any unwanted changes made by the hijacker.
- Delete Temporary Files: Clear your system of temporary files, cache, and cookies. This not only frees up space but also rids your system of potential remnants of the malware.
- Clear Browsing Data: Delete your browsing history, cache, cookies, and saved passwords to ensure the virus is fully eradicated from your system.
- Change Passwords: To strengthen your defence, change passwords for your important accounts. This blocks any unauthorized access and ensures your security moving forward.
- Update Operating System and Software: Ensure your operating system and all software are up to date. Regular updates often include security patches that fortify your system against vulnerabilities.
- Backup and Restore: If the damage is extensive, consider restoring your system to a previous backup point. This wipes out any traces of VenomSoftX and reinstates a clean system.
In the face of Counter. email-service VenomSoftX, proactive measures are your best armour. The digital realm is brimming with innovation, but it also harbours threats that require our vigilance. By following these steps, you’re taking a significant stride toward securing your digital haven. Remember, staying informed and empowered is the key to a safer online experience.
Conclusion:
In the quest for a safe and secure online environment, addressing threats like the counter.wmail-service.com virus is essential. By understanding the risks, staying vigilant against suspicious downloads, and taking prompt action to remove the virus, you can maintain control over your digital space. Regularly updating your security software, practising safe browsing habits, and being cautious about the software you install will go a long way in safeguarding your system against potential threats. Remember, prevention and quick removal are key to maintaining a secure online experience.
Final Thought:
The VenomSoftX malware, often associated with the counter.wmail-service.com virus, serves as a reminder of the ever-present digital threats in today’s interconnected world. By staying informed about such threats and implementing robust cybersecurity practices, you can significantly reduce the risk of falling victim to malware attacks. Stay vigilant, keep your software up to date, and foster a culture of cyber awareness to protect yourself and your digital assets from potential harm